Top 10 Security Risks on the Web (OWASP) and Ways To Address Them Using API Management
Top 10 Security Risks on the Web (OWASP) and Ways To Address Them Using API Management
Critical data stored in the cloud, providing mobile access from anywhere, along with IoT, Open Banking, API-enabled digital platforms, and security—how does it all work?
APIs form the foundation of digital transformation. The proliferation of web applications and digital ecosystems driven by web APIs, though facilitated by the robust capabilities of an API Integration Platform, has heightened security concerns due to their significant exposure. According to a study conducted by Sensedia in collaboration with IDC, security emerged as the most crucial aspect in API strategies, with 85% of large and medium-sized companies prioritizing it.
The Open Web Application Security Project (OWASP) aims to centralize efforts in securing applications and APIs. To achieve this, OWASP conducted a global and collaborative survey to identify the 10 most critical security risks on the web, collectively known as OWASP TOP 10.
The ranking is derived from collected data and community consultations, classifying risks according to the OWASP Risk Rating Methodology. A three-level ranking is assigned based on the following criteria:
- Attack Difficulty (Exploitability)
- Risk Prevalence
- Risk Detection (Detectability)
- Technical Impacts

In the preliminary text (RC1), the inclusion of the item 'Unprotected APIs' in the 2017 rankings was suggested. However, this suggestion was withdrawn because Web APIs are susceptible to several risks mentioned, and creating a separate category did not seem sensible. New references were made to APIs and the API Security Gateway in the revised text.
The modifications to the items in the rankings were as follows:
Topics removed but not forgotten:
- 2013-A8 Cross-site Request Forgery (CSRF)
- 2013-A10 Unvalidated Redirects and Forwards
Topics added:
- 2017-A4 XML External Entity (XXE) or 2017-A8 Insecure Deserialization
- 2017-A10 Insufficient Logging & Monitoring


Classification of risks: May vary based on the unique characteristics of each organization.
In RC1, it is noted that detecting vulnerabilities in APIs can pose greater challenges compared to applications. This difficulty arises from the absence of a user interface (UI) for testing and the utilization of more intricate data structures.
Conversely, APIs frequently establish direct communication with critical systems. When vulnerabilities exist, they may enable unauthorized access and manipulation of sensitive data, potentially leading to complete system hijacking.
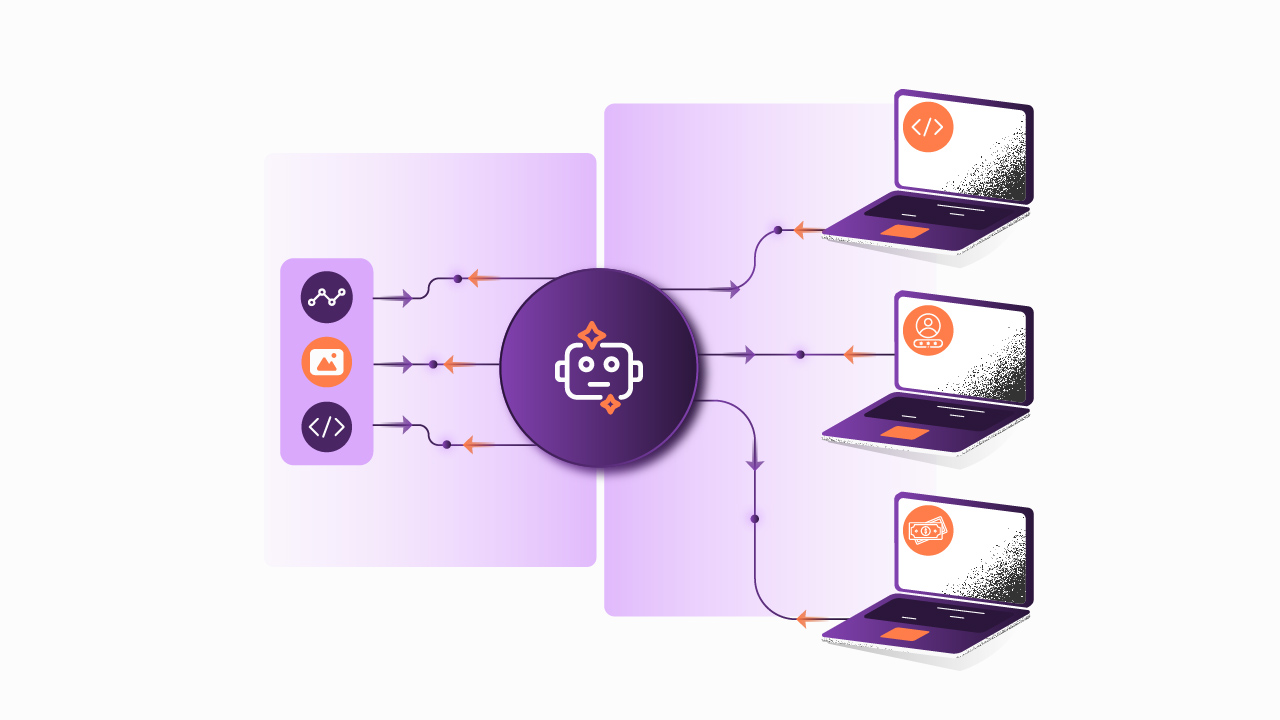
Implementing an API-first strategy using a comprehensive API Management platform also serves as a backup layer for the backend, providing resources for fault detection, supporting the proper design of APIs, and facilitating the separation of environments. Additionally, it enables the implementation of various API security solutions, control, and analysis mechanisms.

A10 OWASP 2017 RC1 – originally included in the partial version but subsequently removed from the final release.
Ranking 2017 OWASP Top 10 Security Risks on the Web
The following outlines the 10 risks from the new OWASP 2017 rankings and the primary methods to mitigate them:
A1 – Injection
Failures resulting from injection, such as SQL injection, occur when malicious data is sent to an interpreter. This data can be interpreted as commands or queries, potentially enabling undesired actions.

How to prevent it?
To thwart this type of attack, it is essential to validate whether the data transmitted by the APIs contains recursive commands in SQL, JSON, XML, or other formats. Additionally, it is crucial to entirely eliminate the use of the interpreter by providing a parameterized interface.
For more information, refer to the Injection Prevention Cheat Sheet by OWASP.
How do we mitigate this risk with an API management platform?
Apply interceptors for SQL threat protection, JSON threat protection, and XML threat protection.
A2 – Authentication Break
Users can compromise authentication through keys, passwords, or cookies, gaining unauthorized access.

How to prevent it?
It is crucial to implement secure communication, utilizing two-way SSL and authentication standards like OAuth.
For further insights, refer to the Authentication Cheat Sheet by OWASP.
How do we mitigate this risk with an API management platform?
Enable two-way SSL communication and OAuth 2.0 authentication.
A3 – Exposure of Sensitive Data
Sensitive data may be exposed if recorded without encryption or when used with weak keys in their generation and management, as well as poor algorithms or hashing techniques.

How to prevent it?
To mitigate this vulnerability, consider implementing log and data obfuscation, encrypting the communication channel, and employing two-way SSL. It is crucial to avoid unnecessarily storing sensitive data and encrypting it both at rest and in transit.
Also, always disable the 'autocomplete' feature on forms and in the cache of sensitive data pages.
Refer to the Cryptographic Storage Cheat Sheet and Transport Layer Protection Cheat Sheet by OWASP for more information.
How do we mitigate this risk with an API management platform?
In addition to implementing two-way SSL communication, initiate Data Obfuscation, Log Obfuscation, and Cryptography.
A4 – XML External Entities (XXE)
Some older XML processors permit the specification of an external entity, encompassing a URI without reference, and are evaluated during XML processing. This vulnerability enables data extraction, server request manipulation, internal systems scanning, and potential DoS attacks, among other risks.

How to prevent it?
Implement corrections or update XML processors, libraries, and their dependencies. Ensure that XML or XSL uploads undergo validation, utilize whitelist input validation, and disable the processing of XXE and DTD. Consider employing virtual patching, API security solutions, or Web Application Firewalls (WAFs).
For more details, refer to the XML External Entity (XXE) Prevention Cheat Sheet by OWASP.
How do we mitigate this risk with an API management platform?
Enable the security gateway API module, create whitelists, and implement interceptors for XML threat protection.
A5 – Access Control with Failure
This occurs when internal references to objects (such as a file, folder, or registry) are without access control, leaving them susceptible to manipulation for unauthorized access.

How to prevent it?
To prevent this issue, create indirect references to objects based on user or session and verify access from unreliable sources when using direct references. Implementing API rate limits can further minimize potential damages.
For additional information, refer to the Access Control – OWASP guide.
How do we mitigate this risk with an API management platform?
Implement authentication using OAuth 2.0, validate access to resources with Plans, and enforce Rate Limit policies using API governance tools.
A6 – Incorrect Security Configuration
Undesired actions may occur when users exploit incorrect security settings.

How to prevent it?
Automatic and periodic API monitoring and scanning is highly useful for detecting issues such as lack of updates, configuration errors, and the use of standardized accounts. Implementing a fast and efficient process for establishing secure environments is crucial, ensuring they remain up-to-date. Maintaining an agile architecture that provides a secure separation of components is also essential.
For further guidance, refer to the Center for Internet Security (CIS): Configuration Guidelines and Benchmarks.
How do we mitigate this risk with an API management platform?
Create and separate environments, define deploy permissions, utilize OAuth 2.0, implement token creation and revocation, centralize management, and conduct audits of events.
A7 – Cross-Site Scripting (XSS)
In XSS attacks, scripts are inserted before data is sent to the browser and executed, enabling session hijacking, redirection to malicious sites, or page defacement.

How to prevent it?
Ensure thorough examination of requests and responses to verify the absence of scripts.
For additional guidance, refer to the XSS (Cross-Site Scripting) Prevention Cheat Sheet by OWASP.
How do we mitigate this risk with an API management platform?
Implement a specific interceptor application for XSS threat protection to verify and block malicious patterns.
A8 – Insecure Deserialization
Distributed applications with public listeners or those relying on client state maintenance may be susceptible to the tampering of serialized data.

How to prevent it?
Avoid accepting serialized objects from untrustworthy sources or serialization that exclusively allows primitive data types. If this is not feasible, implement integrity checks or cryptography in serialized objects to prevent malicious creation of objects or data tampering. Enforce strict-type restrictions during deserialization and before object creation.
Additionally, isolate deserialization code and execute it in environments with minimal privileges or temporary containers. Record exceptions and deserialization failures in logs. Restrict or monitor inbound and outbound connectivity for containers or servers engaged in deserialization, and configure alerts for persistent user deserialization attempts.
For further details, consult the Deserialization Cheat Sheet by OWASP.
How do we mitigate this risk with an API management platform?
Establish whitelists for reliable sources, generate specific logs for each stage of API operations, conduct call tracing, and configure alerts.
A9 – Use of Components with Known Vulnerabilities
Attackers can identify vulnerable components through scanning or manual analysis.

How to prevent it?
Utilize API lifecycle management tools to create an inventory of component versions and dependencies, both server-side and client-side. Monitor component vulnerabilities from public sources like NVD and employ software for automated analysis. Additionally, deactivate unused components, and apply updates and patches from official sources to mitigate exploitable vulnerabilities.
For further information, refer to the National Vulnerability Database (NVD).
How do we mitigate this risk with an API management platform?
Implement the String Match Conditions interceptor to validate calls to URLs with known vulnerabilities.
A10 – Insufficient Logging and Monitoring
Improperly logging faults, a lack of alerts, and the absence of blocking mechanisms enable attackers to test vulnerabilities until an exploitable one is discovered persistently.

How to prevent it?
Utilize widely adopted formats such as REST, GraphQL, and JSON, and implement security mechanisms to ensure secure communication, a robust authentication scheme, access control, and protections against all types of injections.
For more details, refer to the Logging Cheat Sheet by OWASP.
How do we mitigate this risk with an API management platform?
Enable call tracing and logging interceptors, applicable at various processing stages of the APIs. Configure alerts and implement customized API monitoring dashboards.
Sensedia API Platform – Security for your APIs and Backend
Sensedia's API Management Platform has been recognized as Visionary by Gartner and a Strong Performer by Forrester. It provides a range of mechanisms for the protection and analysis of both APIs and backends, offering API lifecycle management tools for resource optimization and development commitment. Additionally, Sensedia offers consulting services for the secure construction of digital strategies and composable architectures based on microservices.

Interested in learning more about how to safeguard your APIs and backend?
Let's discuss it! Feel free to leave your message, and connect with our experts.
Begin your API journey with Sensedia
Hop on our kombi bus and let us guide you on an exciting journey to unleash the full power of APIs and modern integrations.
Embrace an architecture that is agile, scalable, and integrated
Accelerate the delivery of your digital initiatives through less complex and more efficient APIs, microservices, and Integrations that drive your business forward.





.svg)




.png)